G DATA’s security solutions, including Total Security, Internet Security, and Antivirus, emphasize centralized management via My G DATA, offering invoice access and contract details.
Importance of a Well-Designed Data Center
A meticulously planned data center is paramount for sustained business operations, mirroring G DATA’s commitment to robust security. Effective design, like their Advanced Analytics against APT attacks, minimizes downtime and safeguards critical data. Centralized management, as offered by My G DATA, parallels the need for a unified infrastructure overview.
Proper infrastructure ensures scalability, accommodating growth similar to adapting G DATA products for diverse user needs. Redundancy, mirroring G DATA’s layered security, is crucial for resilience. Efficient cooling, like G DATA’s proactive threat detection, prevents equipment failure. A well-designed center optimizes resource utilization, reducing operational costs, and enhancing performance – a principle G DATA applies to its software efficiency.
Ultimately, a robust data center design, akin to G DATA’s award-winning security, fosters trust and reliability, essential for both internal operations and customer confidence. It’s a foundational element for digital success.
Scope of this Data Center Infrastructure Design Guide
This guide comprehensively covers data center infrastructure, mirroring G DATA’s holistic security approach – encompassing power, cooling, networking, and physical security. Like accessing G DATA’s product downloads and handbooks, this resource provides detailed information for planning and implementation.
We will explore UPS systems, power redundancy (N+1, 2N), and scalable power distribution, akin to My G DATA’s centralized management of multiple security features. Cooling technologies, including CRAC units and liquid cooling, will be examined, paralleling G DATA’s proactive threat response. Network topology, high-speed interconnects, and SDN will also be detailed.
Furthermore, the guide addresses physical security measures – access control and fire suppression – reflecting G DATA’s multi-layered protection. Rack infrastructure, server virtualization, and DCIM software are included, offering a complete overview for building and managing a resilient, efficient data center, much like G DATA’s comprehensive security suite.

Power Infrastructure
G DATA’s secure downloads and managed services mirror the need for robust power, ensuring uninterrupted operation and scalability, vital for data center resilience.
UPS (Uninterruptible Power Supply) Systems
G DATA’s commitment to proactive threat defense, exemplified by Advanced Analytics combating APT attacks and recognition from the BSI, parallels the critical role of UPS systems in data centers. These systems provide immediate, temporary power when primary sources fail, preventing data loss and hardware damage. Selecting the appropriate UPS topology – online, offline, or line-interactive – depends on the data center’s criticality and budget.
Redundancy is paramount; employing a modular UPS allows for scalability and hot-swappable components, minimizing downtime during maintenance. Battery technology choices, like lead-acid or lithium-ion, impact lifespan, efficiency, and environmental considerations. Proper sizing is crucial, accounting for current and future power demands, including peak loads and growth projections. Regular testing and maintenance, mirroring G DATA’s continuous software updates, are essential for ensuring UPS reliability and longevity, safeguarding against unexpected power disruptions.
Redundancy in Power Distribution (N+1, 2N)
Similar to G DATA’s layered security approach – encompassing Antivirus, Internet Security, and Total Security – redundant power distribution is fundamental to data center uptime. N+1 redundancy provides one extra power path beyond the required ‘N’, allowing continued operation during a single component failure. This is a cost-effective solution for less critical environments.
2N redundancy, conversely, duplicates all power paths, offering complete isolation and failover capability. This is vital for high-availability applications. Implementing these strategies involves redundant power feeds, automatic transfer switches (ATS), and parallel distribution paths. Careful planning ensures no single point of failure exists. Like My G DATA’s centralized management, a well-designed redundant system simplifies maintenance and troubleshooting. Regular testing, mirroring G DATA’s threat intelligence updates, validates the system’s effectiveness and ensures rapid failover in the event of an outage.
Power Density and Scalability Considerations
Just as G DATA offers scalable security solutions – from basic Antivirus to comprehensive Total Security – data centers must anticipate future power demands. Power density, measured in watts per square foot, is increasing due to more powerful servers and GPUs. Initial designs must accommodate this trend, avoiding oversubscription of power distribution units (PDUs).
Scalability requires modularity. Like the adaptable features within My G DATA, infrastructure should easily expand without significant disruption. This involves pre-provisioning power capacity, utilizing flexible PDU configurations, and planning for future UPS upgrades. Consider the total cost of ownership, balancing upfront investment with long-term scalability. Efficient power distribution, mirroring G DATA’s optimized software, minimizes waste and reduces operational expenses. Proactive monitoring and capacity planning, similar to G DATA’s threat detection, are crucial for sustained performance.
Data Center Cooling Systems
Effective cooling is paramount, much like G DATA’s layered security approach protects against diverse threats. Traditional CRAC (Computer Room Air Conditioning) units remain common, but their efficiency is limited. Modern data centers increasingly adopt strategies to manage heat generated by dense server racks.
Hot Aisle/Cold Aisle Containment directs airflow, maximizing cooling efficiency. More advanced Liquid Cooling Technologies, including direct-to-chip cooling, offer superior heat removal for high-density deployments. Selecting the right cooling system depends on power density, budget, and sustainability goals. Monitoring temperature and humidity, akin to G DATA’s constant system scans, is vital for preventing overheating and ensuring reliable operation. Scalability is key; the cooling infrastructure must adapt as server density increases, mirroring the adaptability of My G DATA’s management portal.
CRAC (Computer Room Air Conditioning) Units
CRAC units are foundational for data center climate control, similar to how G DATA’s core antivirus provides essential protection. These systems deliver cooled air to maintain optimal operating temperatures for servers and networking equipment. Traditional CRAC units circulate air throughout the room, but can be inefficient in high-density environments.
Modern CRAC units often incorporate features like variable speed drives and economizers to improve energy efficiency, mirroring G DATA’s optimization for system resources. Proper placement and airflow management are crucial for maximizing their effectiveness. Regular maintenance, including filter replacements and coil cleaning, is essential for reliable operation. While effective, CRAC units may require supplementation with other cooling technologies, like containment or liquid cooling, to address increasing power densities, much like combining G DATA products for comprehensive security.
Liquid Cooling Technologies

As server densities increase, traditional air cooling, like basic CRAC units, struggles to keep pace, necessitating liquid cooling solutions. These technologies, much like G DATA’s Advanced Analytics combating complex threats, offer superior heat removal capabilities. Direct-to-chip cooling involves circulating coolant directly over processors and other heat-generating components.

Immersion cooling submerges entire servers in a dielectric fluid, providing even greater cooling efficiency. Both methods significantly reduce energy consumption compared to air cooling, aligning with sustainability goals. Implementing liquid cooling requires careful planning, including leak detection systems and compatibility considerations. Similar to managing a G DATA subscription through My G DATA, liquid cooling demands ongoing monitoring and maintenance to ensure optimal performance and prevent disruptions. The initial investment is higher, but the long-term benefits often outweigh the costs.
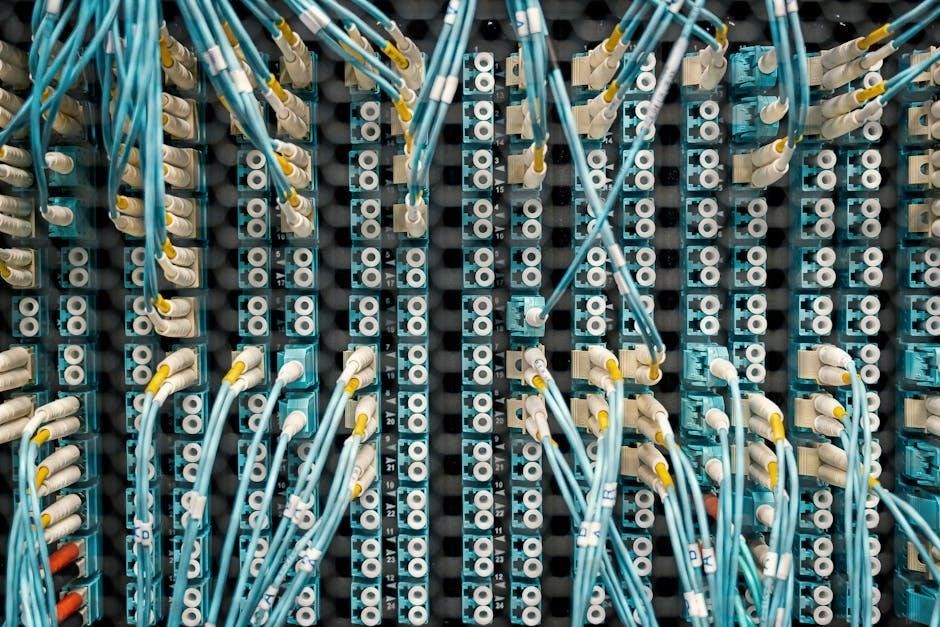
Hot Aisle/Cold Aisle Containment
Hot Aisle/Cold Aisle Containment is a fundamental cooling optimization strategy. It arranges server racks to create distinct airflow paths – cold air intake on one side (cold aisle) and hot air exhaust on the other (hot aisle). This segregation, much like G DATA’s layered security approach, prevents mixing of hot and cold air, increasing cooling efficiency.
Containment systems physically separate the aisles using barriers like doors and roofs, further enhancing airflow control. This reduces the workload on CRAC units and lowers energy costs. Effective containment requires careful rack layout and sealing of any gaps. Monitoring temperature differentials between aisles is crucial, similar to tracking G DATA contract details in My G DATA. Proper implementation minimizes hotspots and ensures consistent server operating temperatures, improving reliability and extending equipment lifespan. It’s a cost-effective method for improving data center cooling performance.
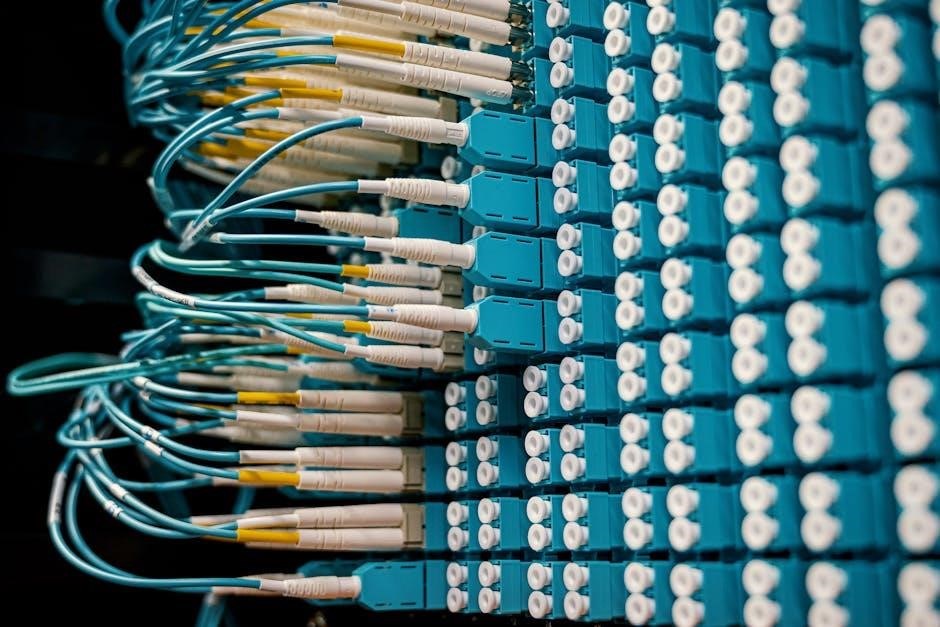
Network Infrastructure
G DATA’s product management portal, My G DATA, offers a centralized view of contracts and invoices, mirroring the need for network oversight.
Data Center Network Topology (Spine-Leaf)
G DATA’s emphasis on robust security, exemplified by Advanced Analytics combating APT attacks and recognition from the BSI, parallels the need for a resilient network foundation.
The spine-leaf architecture represents a modern data center networking paradigm, offering significant advantages over traditional hierarchical designs. This topology consists of two switching layers: a spine and a leaf. Leaf switches connect directly to servers, providing high-bandwidth, low-latency access. Spine switches interconnect all leaf switches, creating a full-mesh fabric.
This design eliminates bottlenecks, enhances scalability, and simplifies management. Every leaf switch has equal connectivity to every spine switch, ensuring predictable performance and minimizing oversubscription. The full-mesh nature provides multiple paths for traffic, enhancing redundancy and fault tolerance, much like G DATA’s layered security approach. Considerations include careful planning of bandwidth allocation and switch capacity to accommodate future growth, mirroring G DATA’s proactive threat detection.
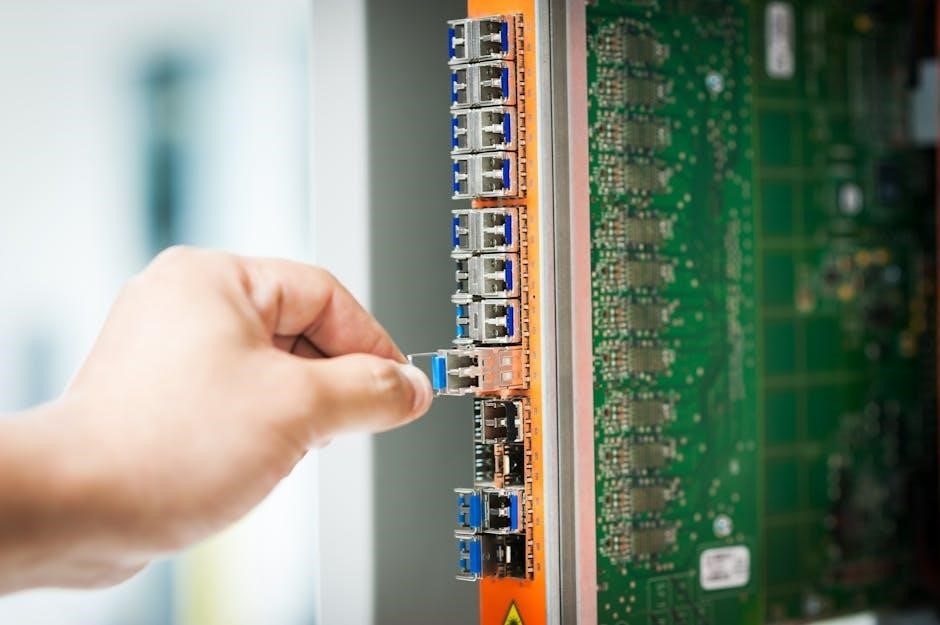
High-Speed Interconnects (400G, 800G)
G DATA’s commitment to cutting-edge technology, like its Advanced Analytics, reflects the data center’s need for high-speed interconnects. As data volumes surge, upgrading interconnects is crucial.
400G and 800G interconnects represent the latest advancements in data transmission, enabling significantly faster data transfer rates within the data center. These technologies utilize advanced modulation techniques and higher-density optical fibers to achieve increased bandwidth. Implementing these interconnects requires careful consideration of transceiver compatibility, fiber optic cabling infrastructure, and switch port capacity.
The benefits include reduced latency, improved application performance, and increased overall network throughput. However, costs associated with 400G/800G technology are currently higher than previous generations. Strategic deployment, focusing on critical workloads, is recommended, similar to G DATA’s targeted threat response. Proper testing and validation are essential to ensure seamless integration and optimal performance, mirroring the rigorous testing of G DATA products.
Network Redundancy and Failover Mechanisms
Inspired by G DATA’s robust security approach, data center network redundancy is paramount for maintaining uptime. Like G DATA protecting against APT-Angriffe, networks need layers of defense against failures.
Implementing redundancy involves duplicating critical network components – switches, routers, and links – to provide backup paths for data transmission. Failover mechanisms automatically switch traffic to redundant paths when a primary component fails. Common techniques include Virtual Router Redundancy Protocol (VRRP) and Spanning Tree Protocol (STP).
Effective failover requires careful configuration and testing. Mechanisms must detect failures quickly and seamlessly redirect traffic without significant disruption. Load balancing distributes traffic across multiple paths to prevent overload and improve performance. Regular drills, similar to G DATA’s security audits, are vital. A well-designed redundant network, like a secure G DATA system, ensures business continuity and minimizes downtime, mirroring the reliability offered by G DATA’s services.
Software-Defined Networking (SDN) in Data Centers
Drawing parallels from G DATA’s centralized management via My G DATA, Software-Defined Networking (SDN) revolutionizes data center network control. SDN decouples the control plane from the data plane, enabling centralized network management and automation.
An SDN controller acts as the brain of the network, dynamically programming network devices – switches and routers – based on application requirements. This allows for agile network provisioning, improved resource utilization, and enhanced security. Like G DATA’s Advanced Analytics combating threats, SDN offers intelligent traffic management.
SDN facilitates network virtualization, creating logical networks on top of the physical infrastructure. This enables multi-tenancy and simplifies network segmentation. Automation capabilities reduce manual configuration errors and accelerate service delivery. The centralized control and programmability of SDN, mirroring G DATA’s portal, offer greater flexibility and efficiency, ultimately optimizing data center operations.
Physical Security
G DATA’s focus on protection, like its Antivirus software, mirrors data center physical security needs: robust access controls and vigilant surveillance systems are crucial.
Access Control Systems (Biometrics, Card Readers)
G DATA’s emphasis on secure access to its My G DATA portal – managing products like Total Security and Internet Security – parallels the layered approach required for data center physical security. Robust access control is paramount, extending beyond simple keycard systems. Multi-factor authentication, incorporating biometrics such as fingerprint or iris scanning, significantly enhances security.
Card readers, while still prevalent, should be integrated with a comprehensive system that tracks and audits all access attempts. Detailed logs are essential for forensic analysis in the event of a breach. Furthermore, access levels must be strictly defined and regularly reviewed, adhering to the principle of least privilege. Integration with video surveillance systems provides a visual record of all physical access events, bolstering accountability and aiding in incident response. The goal is to create a secure perimeter, preventing unauthorized physical access to critical infrastructure.
Surveillance Systems and Monitoring
G DATA’s proactive threat detection, highlighted by its success against APT-Angriffe (Advanced Persistent Threats) recognized by the BSI, mirrors the need for constant vigilance in data center surveillance. Comprehensive monitoring isn’t merely about recording footage; it’s about intelligent analysis. High-resolution IP cameras, strategically positioned throughout the facility, provide complete coverage, including server aisles, access points, and the perimeter.
Video Management Systems (VMS) should incorporate motion detection, object recognition, and anomaly detection capabilities. Real-time alerts notify security personnel of unusual activity. Integration with access control systems correlates physical access events with video recordings. Environmental sensors monitoring temperature, humidity, and smoke further enhance situational awareness. Continuous monitoring, coupled with robust recording and archiving, is crucial for incident investigation and maintaining a secure data center environment.
Data Center Fire Suppression Systems
G DATA’s commitment to robust security, exemplified by its Internet Security suite protecting against Spyware and Trojaner, parallels the critical need for advanced fire suppression in data centers. Traditional sprinkler systems can cause more damage than the fire itself due to water exposure. Therefore, gas-based suppression systems, such as FM-200 or inert gas systems, are preferred.
These systems rapidly extinguish fires without leaving residue or disrupting operations. Early smoke detection systems, utilizing Very Early Smoke Detection Apparatus (VESDA), provide rapid alerts. Fire suppression systems must be integrated with the building’s fire alarm system and monitored 24/7. Regular inspections and maintenance are vital to ensure system reliability. Proper design considers room sealing to maintain agent concentration and minimize collateral damage, safeguarding valuable IT assets.

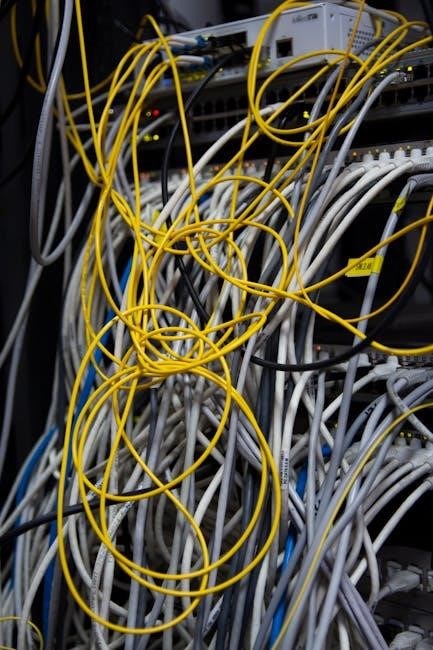
Rack and Server Infrastructure
G DATA’s Advanced Analytics GmbH effectively combats sophisticated APT-Angriffe, mirroring the need for secure and reliable server infrastructure within data centers.
Rack Density and Weight Capacity
G DATA’s comprehensive security suite – encompassing Total Security, Internet Security, and Antivirus for Windows – highlights the importance of robust system protection, mirroring the need for careful consideration of rack density and weight capacity in data center design.
Higher rack densities, while maximizing space utilization, demand meticulous planning. Each rack must support the combined weight of servers, networking equipment, and power distribution units (PDUs). Exceeding weight limits compromises stability and safety.
Furthermore, My G DATA’s centralized management portal, offering organized invoice lists and downloadable PDFs, exemplifies efficient resource allocation. Similarly, data centers require optimized rack layouts to facilitate easy access for maintenance and upgrades.
Consideration must be given to floor loading capacity, rack construction materials, and seismic requirements. Proper weight distribution and adherence to manufacturer specifications are crucial for preventing failures and ensuring long-term reliability. G DATA’s commitment to “Made in Germany” quality reflects a similar dedication to durable and dependable infrastructure.
Server Virtualization and Consolidation
G DATA’s product range – Total Security, Internet Security, and Antivirus – streamlines protection for multiple devices, paralleling the benefits of server virtualization and consolidation within a data center environment.
Virtualization dramatically reduces the physical server footprint, lowering energy consumption and cooling demands. Consolidation maximizes hardware utilization, improving efficiency and reducing capital expenditure. My G DATA’s portal, offering centralized product management and invoice access, embodies this efficiency.
However, successful implementation requires careful planning. Resource allocation must be optimized to prevent performance bottlenecks. Hypervisor selection, storage configuration, and network bandwidth are critical considerations.
Furthermore, robust backup and disaster recovery strategies are essential to protect virtual machines. G DATA’s advanced analytics, combating APT attacks, mirrors the need for proactive security measures in virtualized environments. Proper monitoring and management tools are vital for maintaining stability and ensuring optimal performance, much like the detailed reporting available through G DATA’s services.
Blade Server Technology
G DATA’s focus on streamlined security, exemplified by Internet Security and Antivirus solutions, resonates with the core principles of blade server technology – density and efficiency.
Blade servers pack significant computing power into a compact form factor, reducing rack space and simplifying cabling. This high density lowers infrastructure costs and improves manageability. Like My G DATA’s centralized portal for managing licenses and invoices, blades offer a consolidated approach.
However, blade systems require specialized infrastructure, including dedicated chassis, power supplies, and networking modules. Cooling becomes a critical concern due to the concentrated heat output. Careful planning is essential to ensure adequate airflow and prevent overheating.
Furthermore, shared infrastructure components introduce potential single points of failure. Redundancy is paramount, requiring redundant power supplies, fans, and network connections. G DATA’s proactive threat detection, particularly against APT attacks, parallels the need for robust redundancy in blade server deployments, ensuring continuous operation and data protection.

Data Center Management and Monitoring
G DATA’s Advanced Analytics combats APT attacks, mirroring the need for robust monitoring; My G DATA provides centralized control and detailed reporting.
DCIM (Data Center Infrastructure Management) Software
DCIM software is pivotal for modern data center operations, offering a holistic view of the physical infrastructure. Similar to My G DATA’s centralized management portal, DCIM tools consolidate monitoring and control into a single platform. This includes real-time data on power usage, cooling efficiency, and environmental conditions – mirroring G DATA’s focus on comprehensive security oversight.
Effective DCIM solutions provide asset tracking, capacity planning, and change management capabilities. They enable proactive identification of potential issues, reducing downtime and optimizing resource allocation. Just as G DATA provides detailed invoice lists and contract information, DCIM offers granular visibility into data center assets and their lifecycle. The ability to download reports in formats like PDF, akin to My G DATA’s functionality, is crucial for documentation and analysis.
Furthermore, DCIM integrates with other IT management systems, fostering automation and streamlining workflows. This holistic approach, much like G DATA’s integrated security suite, enhances overall operational efficiency and reduces the risk of human error.
Environmental Monitoring (Temperature, Humidity)
Maintaining optimal environmental conditions within a data center is paramount for reliability, mirroring G DATA’s commitment to consistent security performance. Precise temperature and humidity control prevents equipment overheating and corrosion, extending lifespan and minimizing failures. This proactive approach, similar to G DATA’s advanced threat detection, safeguards against potential disruptions.
Sophisticated monitoring systems provide real-time data and alerts, enabling swift responses to deviations from pre-defined thresholds. Just as My G DATA offers a centralized view of security events, environmental monitoring provides a comprehensive overview of data center conditions. Detailed logging and reporting, with downloadable PDF summaries, facilitate analysis and capacity planning – echoing G DATA’s invoice access feature.
Integration with DCIM software allows for correlated analysis of environmental data with other infrastructure metrics, optimizing cooling efficiency and reducing energy consumption. This holistic view, akin to G DATA’s integrated security suite, enhances overall data center management.
Remote Infrastructure Management
Remote Infrastructure Management (RIM) offers centralized control and monitoring of data center resources, mirroring the convenience of My G DATA’s portal for product management. This capability is crucial for organizations with geographically dispersed data centers or limited on-site IT staff, ensuring consistent operational standards, much like G DATA’s globally consistent security updates.
RIM solutions enable proactive issue resolution, reducing downtime and improving service levels. Secure remote access, coupled with robust authentication – similar to G DATA’s multi-layered security approach – safeguards against unauthorized access. Detailed reporting and analytics, downloadable in PDF format, provide valuable insights into infrastructure performance and capacity utilization.
Automated workflows and orchestration tools streamline routine tasks, freeing up IT personnel to focus on strategic initiatives. This efficiency gain parallels G DATA’s automated threat response capabilities, enhancing overall operational effectiveness and reducing the burden on IT teams.